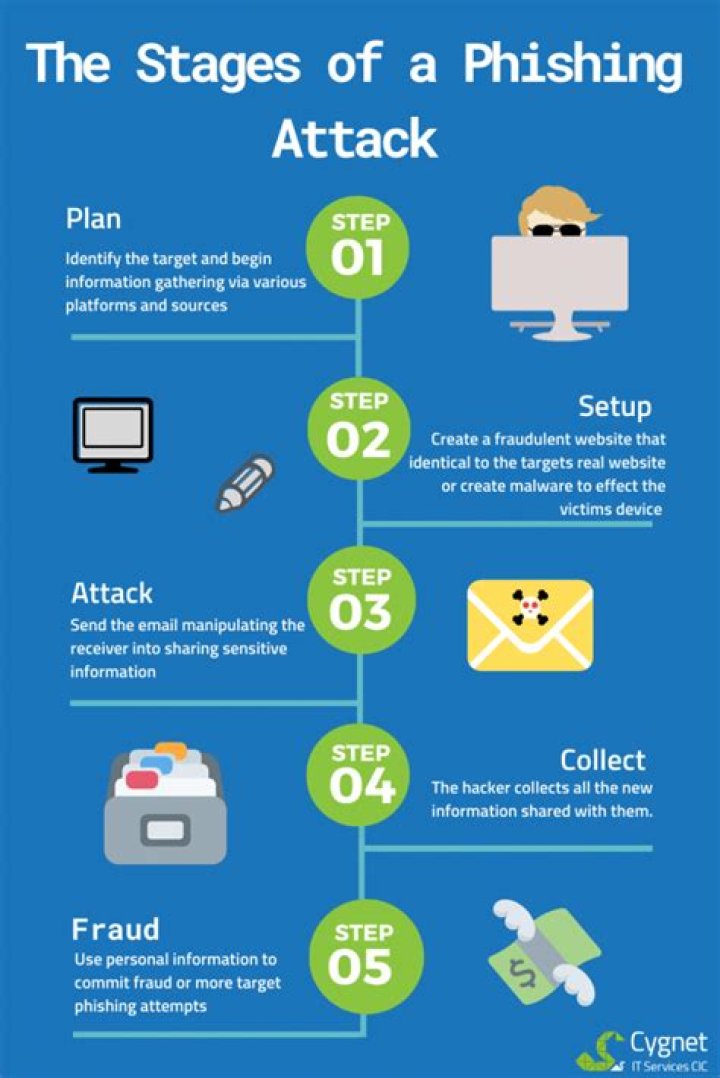
A spear phishing attack begins with the cyber criminal finding information about the target, then using that target to build a connection, and thirdly using that connection to make the target perform an action.
What are the 3 types of phishing?
- Spear Phishing.
- Whaling.
- Vishing.
- Email Phishing.
What are 5 features of phishing?
- The email makes unrealistic threats or demands. Intimidation has become a popular tactic for phishing scams. …
- There’s a catch. …
- Poor spelling and grammar. …
- A mismatched or dodgy URL. …
- You are asked for sensitive information.
What are the 4 steps to protect yourself from phishing attacks?
- Protect your computer by using security software. …
- Protect your mobile phone by setting software to update automatically. …
- Protect your accounts by using multi-factor authentication. …
- Protect your data by backing it up.
What are examples of phishing attacks?
- Phishing Email. Phishing emails still comprise a large portion of the world’s yearly slate of devastating data breaches. …
- Spear Phishing. …
- Link Manipulation. …
- Fake Websites. …
- CEO Fraud. …
- Content Injection. …
- Session Hijacking. …
- Malware.
How many types of phishing are there?
With a better understanding of the twelve types of phishing attacks and how to identify them, organizations can protect their users and their data more effectively.
What involves phishing?
Phishing attacks are the practice of sending fraudulent communications that appear to come from a reputable source. It is usually done through email. The goal is to steal sensitive data like credit card and login information, or to install malware on the victim’s machine.
What methods do you employ to protect yourself against spam and phishing?
- Set up multiple email addresses. It’s a good idea to have at least two email addresses: …
- Never respond to any spam. Most spammers verify receipt and log responses. …
- Think before you click ‘unsubscribe’ …
- Keep your browser updated. …
- Use anti-spam filters.
What are four indications of a suspicious email?
- An Unfamiliar Tone or Greeting. …
- Grammar and Spelling Errors. …
- Inconsistencies in Email Addresses, Links & Domain Names. …
- Threats or a Sense of Urgency. …
- Suspicious Attachments.
Phishing is a type of cybersecurity attack during which malicious actors send messages pretending to be a trusted person or entity. … Social engineering attacks, like phishing, are often combined with other threats, such as malware, code injection, and network attacks.
Article first time published onWhy is it called phishing?
Some say the term phishing got influences from the word fishing. Analogous to fishing, phishing is also a technique to “fish” for usernames, passwords, and other sensitive information, from a “sea” of users. Hackers generally use the letter “ph” instead of “f” and therefore initially they were known as phreaks.
What methods are used in phishing attacks?
- Using legitimate links. Most email filters scan for known phishing URLs. …
- Mixing legitimate and malicious code. …
- Abusing redirections and URL shorteners. …
- Obfuscating brand logos. …
- Confusing the filter with little content or excess noise.
What are phishing techniques?
Phishing is a type of social engineering attack often used to steal user data, including login credentials and credit card numbers. It occurs when an attacker, masquerading as a trusted entity, dupes a victim into opening an email, instant message, or text message.
What are the three elements of cybersecurity?
When we discuss data and information, we must consider the CIA triad. The CIA triad refers to an information security model made up of the three main components: confidentiality, integrity and availability. Each component represents a fundamental objective of information security.
What are 4 common indications that an email is a phishing attempt?
- The message is in your spam folder. …
- It is an unsolicited message. …
- Important information is in an attachment. …
- Urgent action is required and there is a threat in the email. …
- You are asked to click a link in an email.
What steps would you take to identify a phishing email?
- Emails with Bad Grammar and Spelling Mistakes.
- Emails with an Unfamiliar Greeting or Salutation.
- Inconsistencies in Email Addresses, Links & Domain Names.
- Suspicious Attachments.
- Emails Requesting Login Credentials, Payment Information or Sensitive Data.
- Too Good to Be True Emails.
How do you tell if an email is a phishing attempt?
- The message is sent from a public email domain. No legitimate organisation will send emails from an address that ends ‘@gmail.com’. …
- The domain name is misspelt. …
- The email is poorly written. …
- It includes suspicious attachments or links. …
- The message creates a sense of urgency.
What are three things you can do to protect against phishing?
- Employ common sense before handing over sensitive information. …
- Never trust alarming messages. …
- Do not open attachments in these suspicious or strange emails — especially Word, Excel, PowerPoint or PDF attachments.
What are the steps would you recommend to person to avoid phishing?
Anti-spyware and firewall settings should be used to prevent phishing attacks and users should update the programs regularly. Firewall protection prevents access to malicious files by blocking the attacks. Antivirus software scans every file which comes through the Internet to your computer.
What are some of the best ways you can protect your users against phishing attacks?
As an administrator, you can help your users avoid phishing attacks by implementing the Password Alert extension to users of your domain. Password Alert will detect if users enter their Google password into any web sites other than the Google Sign in page accounts.google.com.
What is the PH in phishing?
Its “ph” spelling is influenced by an earlier word for an illicit act: “phreaking.” Phreaking involves fraudulently using an electronic device to avoid paying for telephone calls, and its name is suspected of being a shortening of “phone freak.” A common phishing scam involves sending e-mails that appear to come from …
What is the first form of phishing called?
Some of the earliest hackers were known as phreaks. Phreaking refers to the exploration, experimenting and study of telecommunication systems. Phreaks and hackers have always been closely linked. The “ph” spelling was used to link phishing scams with these underground communities.
Can antivirus detect phishing?
The antivirus software can block offending e-mails that come from a suspect source or contain phrases common to many phishing attempts. Antivirus software like Norton 360 can also warn subscribers when they’ve stumbled upon a unreliable Web site.
What are the different ways to do phishing?
- Email Phishing. …
- Spear Phishing. …
- Whaling. …
- Smishing. …
- Vishing. …
- Business Email Compromise (CEO Fraud) …
- Clone Phishing. …
- Evil Twin Phishing.
What are different phishing techniques?
Phishing conducted via Short Message Service (SMS), a telephone-based text messaging service. A smishing text, for example, attempts to entice a victim into revealing personal information via a link that leads to a phishing website.
What is phishing explain types of phishing?
Phishing attacks are the practice of sending fraudulent communications that appear to come from a reputable source. It is usually done through email. The goal is to steal sensitive data like credit card and login information, or to install malware on the victim’s machine.
What is the difference between phishing and spam?
Spam is unsolicited email, instant messages, or social media messages. … Phishing is an email sent from an Internet criminal disguised as an email from a legitimate, trustworthy source.
What are the 3 elements of good cyber security?
- Assessing your organization’s current cybersecurity program and its prioritization.
- Remediating endpoints at scale, bringing them into compliance with security best practices.
- Implementing cybersecurity policies and monitoring them to stay in compliance.
What are the three aspects of security?
Understanding the significance of the three foundational information security principles: confidentiality, integrity, and availability.
What are the three foundational principles of the cybersecurity domain choose three?
Explanation: Three foundational security principles are confidentiality, integrity and availability.