The software attack surface is the complete profile of all functions in any code running in a given system that are available to an unauthenticated user. The more surface there is, the better the chance an attacker or a piece of malware can use various exploits to gain access and run code on the target machine.
What are the three types of software attacks?
Not all cyber attacks are created equal and in this post we hope to shed some light on the “Big 3” types of cyber attacks, malware, ransomware, and phishing attacks.
What are software attacks in cyber security?
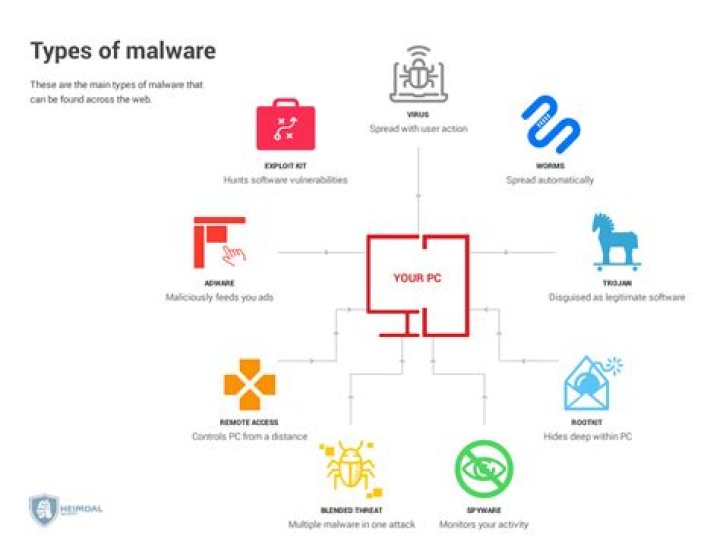
Software attacks means attack by Viruses, Worms, Trojan Horses etc. … So Malware basically means malicious software that can be an intrusive program code or anything that is designed to perform malicious operations on system.
What are the common types of software attacks?
- Malware. Malware is a term used to describe malicious software, including spyware, ransomware, viruses, and worms. …
- Phishing. …
- Man-in-the-middle attack. …
- Denial-of-service attack. …
- SQL injection. …
- Zero-day exploit. …
- DNS Tunneling.
What is an example of attack?
An example of attack is mold growing inside the walls of a house. An example of attack is a man holding a gun to a woman’s head, and demanding her purse and jewelry. Attack is defined as the act of making a physical or verbal attempt to hurt or destroy, sometimes in a purposefully hurtful manner.
What are network attacks?
Network attacks are unauthorized actions on the digital assets within an organizational network. Malicious parties usually execute network attacks to alter, destroy, or steal private data. Perpetrators in network attacks tend to target network perimeters to gain access to internal systems.
What are the 4 types of attacks in a software?
- Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks. …
- Man-in-the-middle (MitM) attack. …
- Phishing and spear phishing attacks. …
- Drive-by attack. …
- Password attack. …
- SQL injection attack. …
- Cross-site scripting (XSS) attack. …
- Eavesdropping attack.
What is cyber attacks with examples?
Cyber attacks most commonly involve the following: Malware, in which malicious software is used to attack information systems. Ransomware, spyware and Trojans are examples of malware. … It is also sometimes called an eavesdropping attack.What are the top 10 types of cyber attacks?
- Malware. The term “malware” encompasses various types of attacks including spyware, viruses, and worms. …
- Phishing. …
- Man-in-the-Middle (MitM) Attacks. …
- Denial-of-Service (DOS) Attack. …
- SQL Injections. …
- Zero-day Exploit. …
- Password Attack. …
- Cross-site Scripting.
Malware is intrusive software that is designed to damage and destroy computers and computer systems. Malware is a contraction for “malicious software.” Examples of common malware includes viruses, worms, Trojan viruses, spyware, adware, and ransomware.
Article first time published onWhat is attacks and its types?
Endpoint attacks—gaining unauthorized access to user devices, servers or other endpoints, typically compromising them by infecting them with malware. Malware attacks—infecting IT resources with malware, allowing attackers to compromise systems, steal data and do damage. These also include ransomware attacks.
How do cyber attacks work?
How are cyber attacks carried out? Many cyber attacks are opportunistic, with hackers spotting vulnerabilities in a computer system’s defences and exploiting them. This may involve finding flaws in the code of a website, that allows them to insert their own code and then bypass security or authentication processes.
How do cyber attacks happen?
A cyber attack is any action taken by cybercriminals with malicious goals in mind. Cybercriminals launch their attacks using one or more computers to strike other computers, networks or information systems. A variety of methods can be used to launch a cyber attack, but the goals is commonly to: Steal data.
What are the 5 types of cyber attacks?
- 1- Denial of Service (DoS) attack and Distributed Denial of Service (DDoS) attack. …
- 2- Malware. …
- 3- Phishing. …
- 4- Dive by Download. …
- 5- Password cracking. …
- 6- Structures Query Language. …
- 7- Man in the Middle (MitM) …
- 8- Cross-site scripting.
What are the 8 types of computer attacks?
- Phishing & Social Engineering Attacks. …
- Password Attacks & Credential Reuse. …
- Denial-of-Service Attacks. …
- Man-in-the-Middle (MitM) …
- SQL Injections. …
- Zero-day Exploit. …
- Cross-site Scripting (XSS) …
- Drive-by-downloads.
What are the 6 types of malware?
- Virus. Viruses are designed to damage the target computer or device by corrupting data, reformatting your hard disk, or completely shutting down your system. …
- Worm. …
- Trojan Horse. …
- Spyware. …
- Adware. …
- Ransomware.
How do I remove malware?
- Reboot in safe mode.
- Uninstall all suspicious apps.
- Get rid of pop-up ads and redirects from your browser.
- Clear your downloads.
- Install a mobile anti-malware app.
Can malware steal files?
What Can Malware Do? In short, malware can wreak havoc on a computer and its network. Hackers use it to steal passwords, delete files and render computers inoperable.
What is the main purpose of cyberwarfare?
According to the Cybersecurity and Infrastructure Security Agency, the goal of cyberwarfare is to “weaken, disrupt or destroy” another nation.
How can cyber attacks be prevented?
Prevention is the key to reducing the risk of a data breach. By investing in cybersecurity software, using a VPN, and being aware of common attack methods, individuals and organizations can deter hackers and keep their data private.