A checkpoint is used for recovery if there is an unexpected shutdown in the database. Checkpoints work on some intervals and write all dirty pages (modified pages) from logs relay to data file from i.e from a buffer to physical disk. It is also known as the hardening of dirty pages.
How does a checkpoint mechanism help in database recovery explain through an example?
The checkpoint is a type of mechanism where all the previous logs are removed from the system and permanently stored in the storage disk. … When it reaches to the checkpoint, then the transaction will be updated into the database, and till that point, the entire log file will be removed from the file.
What is the use of checkpoint?
A checkpoint, in a virtualization context, is a snapshot of the state of a virtual machine. Like a restore point in Windows operating systems, a checkpoint allows the administrator to return the virtual machine to a previous state. Checkpoints are most commonly used to create backups before conducting updates.
What are checkpoints in database?
A database checkpoint is a test operation that verifies data retrieved from the database by comparing that data with the baseline copy stored in your project. That may be needed, for example, when you test an application that modifies a database and want to verify that the appropriate tables are updated correctly.What is the advantage of taking checkpoints of a database?
A Database Storage Checkpoint keeps track of block change information and thereby enables incremental database backup at the block level. A Database Storage Checkpoint helps recover data from incorrectly modified files.
What is SQL checkpoint?
A checkpoint creates a known good point from which the SQL Server Database Engine can start applying changes contained in the log during recovery after an unexpected shutdown or crash.
What is checkpoint recovery?
Checkpoint-Recovery is a common technique for imbuing a program or system with fault tolerant qualities, and grew from the ideas used in systems which employ transaction processing [lyu95]. It allows systems to recover after some fault interrupts the system, and causes the task to fail, or be aborted in some way.
What are the types of checkpoint?
There are four types of Checkpoints that the SQL Server Database Engine supports: Internal, Manual, Automatic and Indirect.How does Checkpoint work in SQL Server?
Checkpoint is a process that writes current in-memory dirty pages (modified pages) and transaction log records to physical disk. In SQL Server checkpoints are used to reduce the time required for recovery in the event of system failure. Checkpoint is regularly issued for each database.
What is checkpoint describe the role of checkpoints in testing?A checkpoint is a comparison (or verification) operation that is performed during testing. These operations are an essential part of the testing process as they check whether the tested application functions properly.
Article first time published onWhat are checkpoints in ETL?
Checkpoints are basically points in your transformation where you persist the current state of the data within the transformation.
What is a checkpoint in DBMS when does checkpoint occur in DBMS?
Checkpoint is a mechanism where all the previous logs are removed from the system and stored permanently in a storage disk. Checkpoint declares a point before which the DBMS was in consistent state, and all the transactions were committed.
What is difference between checkpoint and lazy writer?
The Lazy writer process also flushes out the dirty pages to the disk. There is a difference between the SQL Server CHECKPOINT and the Lazy writer process. CHECKPOINT does not remove the dirty pages from the memory. The dirty pages after written to disk are marked as Clean and stay in the buffer cache.
What is checkpoint and rollback?
Checkpointing and rollback-recovery are well-known techniques that allow processes to make progress in spite of failuresi2. The failures under consideration are tran- sient problems such as hardware errors and transaction aborts, i.e., those that are unlikely to recur when a process restarts.
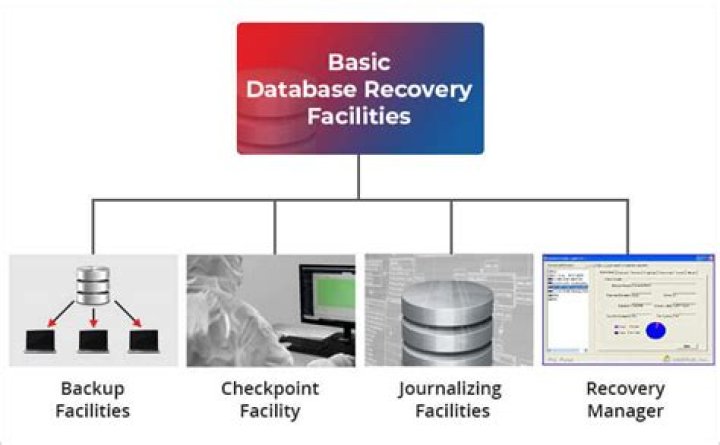
What are database recovery techniques?
The techniques used to recover the lost data due to system crash, transaction errors, viruses, catastrophic failure, incorrect commands execution etc. are database recovery techniques. So to prevent data loss recovery techniques based on deferred update and immediate update or backing up data can be used.
What are the two kinds of checkpoints for checkpoint algorithm?
There are two main approaches for checkpointing in the distributed computing systems: coordinated checkpointing and uncoordinated checkpointing. In the coordinated checkpointing approach, processes must ensure that their checkpoints are consistent.
How do you stop a checkpoint in SQL Server?
AFAIK, the only way to stop the CHECKPOINT process is to stop the SQL Server service.
What is TUF file in SQL Server?
TUF file is a Microsoft SQL Server Transaction Undo file. The TUF file basically contains the information with respect to any modifications that were made as part of incomplete transactions at the time the backup were performed. A transaction undo (. TUF) file is required if a database is loaded in read-only state.
What is dirty page in SQL?
In SQL Server, the data in table is stored in pages which has fixed size of 8 KB. … Once a page is modified in memory due to data modification (Insert/update/delete), it is called “dirty” page. On the other hand, if a page which is not modified is called “clean” page.
What is checkpoint in SSIS and how do you configure a checkpoint?
We can configure a CHECKPOINT file in the SSIS package to log package execution information in it. If the package execution fails, SSIS uses the information in the checkpoint file to restart it from the point of failure. Once the package successfully executes, it removes the checkpoint file.
What are the types of checkpoints in Oracle?
- Full Checkpoint.
- Thread Checkpoint.
- File Checkpoint.
- Object “Checkpoint”
- Parallel Query Checkpoint.
- Incremental Checkpoint.
- Log Switch Checkpoint.
What is fuzzy checkpoint in DBMS?
In fuzzy checkpointing, at the time of checkpoint, all the active transactions are written in the log. … The transactions that have been committed before checkpoint are written to the disk and hence need not be redone.
What is bitmap checkpoint?
Bitmap Checkpoint helps a user in checking the bitmap of an image or a full web page. It does a pixel by pixel comparison between actual and expected images. Image Checkpoint enables you to check properties like source file location of a web image.
What is checkpoint in automation?
A checkpoint is an automated comparison that you can have within an automated test. When the test is run, the checkpoint compares the value stored in the test (i.e. the baseline value) with the actual value and reports success or failure depending on the comparison.
What is a standard checkpoint?
A standard checkpoint takes a snapshot of the virtual machine and virtual machine memory state, but is not a full backup of the VM. … Standard checkpoints capture the state, data and hardware configuration of a running virtual machine, and are intended for use in development and test scenarios.
What is the difference between ETL and ELT?
KEY DIFFERENCE ETL stands for Extract, Transform and Load while ELT stands for Extract, Load, Transform. ETL loads data first into the staging server and then into the target system whereas ELT loads data directly into the target system.
What is a good ETL?
- 1) Xplenty. Xplenty is a cloud-based ETL and ELT (extract, load, transform) data integration platform that easily unites multiple data sources. …
- 2) Talend. Talend Data Integration is an open-source ETL data integration solution. …
- 3) FlyData. …
- 4) Informatica PowerCenter. …
- 5) Oracle Data Integrator. …
- 6) Stitch. …
- 7) Fivetran.
How do you practice ETL?
- COPY data from multiple, evenly sized files.
- Use workload management to improve ETL runtimes.
- Perform table maintenance regularly.
- Perform multiple steps in a single transaction.
- Loading data in bulk.
- Use UNLOAD to extract large result sets.
What is the importance of database recovery in DBMS?
If such a failure affects the operation of a database system, you must usually recover the database and return to normal operation as quickly as possible. Recovery should protect the database and associated users from unnecessary problems and avoid or reduce the possibility of having to duplicate work manually.
How many types of recovery techniques are in database?
There are three basic types of recovery: instance recovery, crash recovery, and media recovery.
When a dirty buffer is generated which type of checkpoint is done?
Incremental checkpointing DBWR checks at least every three seconds to determine whether it has work to do. When DBWn writes dirty buffers, it advances the checkpoint position, causing CKPT to write the checkpoint position to the control file, but not to the data file headers. . . .